APU’s computer technology affiliate diploma program is a less math- and theory-intensive approach and it’s ideally fitted to those with pursuits in computer and community assist, IT and technical assist, and database and system administration. The program will allow you to enrich the trade certifications needed for many IT jobs, such as Security+ and A+, with a degree. Maricopa Community Colleges also makes it easy for you to transfer to a four-year program through our partnerships with over 40 colleges and universities nationwide. With the widespread use of computer systems all over the world, there’s an ongoing need for skilled computer specialists. The affiliate degree in Computer Technology – Programming prepares students for entry-level positions in an enormous number of industries. This diploma offers expertise in a variety of programming languages, similar to Phython, C#, Java, PHP, HTML, Mobile Apps, and SQL. Graduates will be geared up to search out employment as business-application programmers, database managers, and system analysts.
- This course is an introductory study of Web analytics technology and how businesses and organizations could to use the technology to measure website traffic, enhance business presence, and conduct market analysis.
- Hard disk drives, floppy disk drives and optical disc drives function both enter and output gadgets.
- Select the most feasible different voice and knowledge communications technologies for specific business functions from the varied applied sciences obtainable.
It just isn’t universally true that bugs are solely as a result of programmer oversight. Computer hardware may fail or might itself have a basic problem that produces unexpected leads to certain conditions. For occasion, the Pentium FDIV bug triggered some Intel microprocessors in the early Nineties to provide inaccurate outcomes for certain floating point division operations. This was brought on by a flaw in the microprocessor design and resulted in a partial recall of the affected devices. High level languages are additionally typically interpreted rather than compiled.
University Assets
Configure and help networks in a peer to peer community and a shopper server, domain-based network structure. Install, configure and troubleshoot quite a lot of shopper and server platform working methods.
As the usage of computers has spread throughout society, there are an growing variety of careers involving computer systems. While a person will normally learn every word and line in sequence, they may at occasions leap again to an earlier place within the text or skip sections that aren’t of interest. Similarly, a pc might sometimes go back and repeat the instructions in some section of this system again and again until some inner condition is met. This known as the move of management inside the program and it’s what permits the pc to perform tasks repeatedly with out human intervention.
A Career In Computer Technology
Plan, analysis, create, and revise spreadsheets and databases for a particular enterprise application. Discuss rising Computer & Technology subjects in business related to data evaluation and mangement.
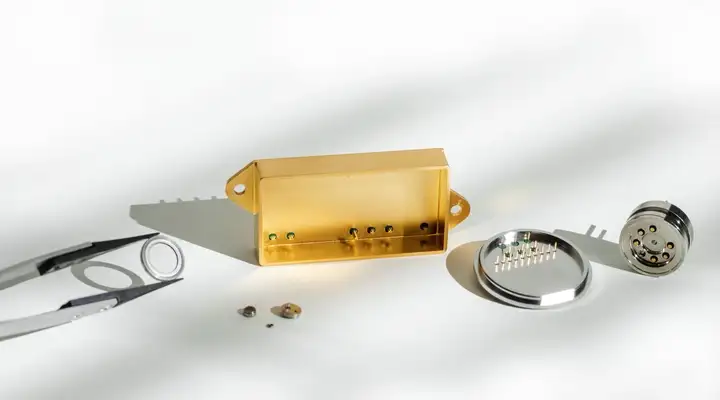
The Antikythera Mechanism is an ancient Greek astronomical computer of amazing complexity – HODINKEE
The Antikythera Mechanism is an ancient Greek astronomical computer of amazing complexity.
Posted: Thu, 05 Aug 2021 13:00:00 GMT [source]
This course is a examine of the applicable abilities and technology essential to application software integration. Students will discover the rules, practices, options, and functions of application software program processing within the Microsoft Office Suite. The course will be taught with a combination of analytical methods and practical Computer exercises. The course will allow students to experience a extra comprehensive understanding of generally used applications software and the way they combine to offer options. Students could entry MS Office 365 Suite through their MyCampus account for FREE within the classroom.
Accessibility Statement
This course will present essential steering to build a proper audit to make certain that operational integrity and customer information protection, among other aspects, are addressed for cloud based mostly resources. This course will serve as a cloud computing reference for auditors and IT Security Professionals. It may even present data to assist in getting ready for an audit addressing cloud computing. Apply key ideas of cloud computing and the security and privacy involved with this technology. Those interested in the computer or IT industry, but needing a much less math- or theory-intensive method, will discover American Public University’s bachelor of computer technology program an acceptable means towards that objective. The program emphasizes certification preparation and hands-on learning. Section 508 is a federal legislation that requires businesses to provide individuals with disabilities equal access to electronic data and data similar to those who don’t have disabilities except an undue burden can be imposed on the agency.
In this course, we consider and talk about how ethical theories and ideas can inform and provide steerage about interactions and makes use of of computing technologies. Topics embrace the event interpretation, and software of ethical principle, moral values, private duty, codes of conduct, ethics in the true and virtual worlds, mental property, and information security. Students are supplied with steerage and opportunities for enhancing informal and formal writing abilities. Grades received Technology on writing assignments will represent a major factor of the final course grade. This course teaches the coed the essential applied sciences wanted by NSSA majors, focused on PC and mainframe hardware matters. They embody how those platforms function, how they are configured, and the operation of their major inner parts. Also covered are the essential operating system interactions with those platforms, bodily security of property, and computing-centric mathematical concepts.


More Stories
Why Do You Need Digital Marketing for Business?
7 Reasons Why Your Business Needs A Digital Marketing Strategy
Why Business Owners Seek to Enter Foreign Markets